A local area network (LAN) is a collection of devices connected together in one physical location, such as a building, office, or home. A LAN can be small or large, ranging from a home network with one user to an enterprise network with thousands of users and devices in an office or school.
Regardless of size, a LAN’s single defining characteristic is that it connects devices that are in a single, limited area. In contrast, a wide area network (WAN) or metropolitan area network (MAN) covers larger geographic areas. Some WANs and MANs connect many LANs together.
A LAN comprises cables, access points, switches, routers, and other components that enable devices to connect to internal servers, web servers, and other LANs via wide area networks.
The rise of virtualization has also fueled the development of virtual LANs, which enable network administrators to logically group network nodes and partition their networks without a need for major infrastructure changes.
For example, in an office with multiple departments, such as accounting, IT support, and administration, each department’s computers could be logically connected to the same switch but segmented to behave as if they are separate.
Types of LAN
Ethernet is the most common type of LAN. Different Lan can be differentiated on the behalf of following characteristics.
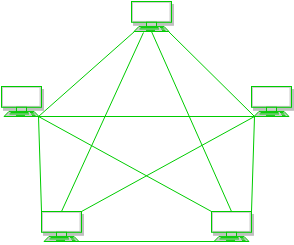
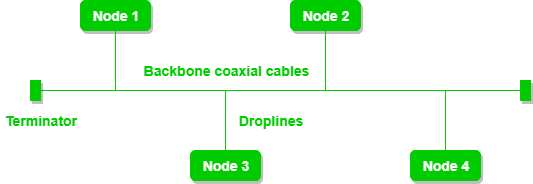
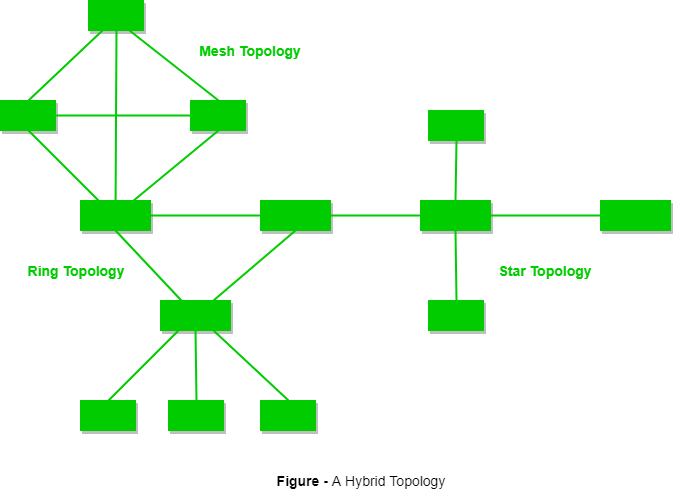
- Topology: The topology is the geometric arrangement of a network elements. For example, Network devices can be interconnected in a ring topology or in a bus topology or linear bus.
- Protocols: It is a guidelines for communicating data between two devices. The protocols also determine type of error and data compression.
- Media: The cable used in Lan to connect devices are twisted-pair wire, coaxial cables, or fiber optic.
Benefits of a LAN
The advantages of a LAN are the same as those for any group of devices networked together. The devices can use a single Internet connection, share files with one another, print to shared printers, and be accessed and even controlled by one another.
LANs were developed in the 1960s for use by colleges, universities, and research facilities (such as NASA), primarily to connect computers to other computers. It wasn’t until the development of Ethernet technology (1973, at Xerox PARC), its commercialization (1980), and its standardization (1983) that LANs started to be used widely.
While the benefits of having devices connected to a network have always been well understood, it wasn’t until the wide deployment of Wi-Fi technology that LANs became commonplace in nearly every type of environment. Today, not only do businesses and schools use LANs, but also restaurants, coffee shops, stores, and homes.
Wireless connectivity has also greatly expanded the types of devices that can be connected to a LAN. Now, nearly everything imaginable can be “connected,” from PCs, printers, and phones to smart TVs, stereos, speakers, lighting, thermostats, window shades, door locks, security cameras–and even coffeemakers, refrigerators, and toys.
The Evolution of LAN
As there is a tremendous use of PC or desktop computers in the office environment, it became apparent that attaching a printer or FAX machine to each and every computer is highly expensive. Further, copying files to a disk and moving from one computer to another to print the file is also time consuming. Connecting computers so that they could share a printer and share files translated into big savings.
In 1982, 10 Mbps Ethernet cards came into existence and they were very expensive. By 1988, 10 Mbps Ethernet had acceptable performance for large LANs and was still good for small installations. By 1990, large installations were beginning to see congestion. Hence, alternatives to 10 Mbps cards were becoming popular. One of these alternatives was to install a switched architecture, rather than constructing architecture with hubs.
In 1996, 10Mbps switched LANs were providing acceptable service for smaller installations. The awesome technology at this point was 100Mbps shared Ethernet. By 1998 switched 10Mbps Ethernet was common in small LANs and switched 100 Mbps Ethernet was common in large LANs. Large LANs are beginning to see limitations of 100 Mbps when everyone on the LAN starts doing video conferencing.
Now, Gigabyte Ethernet cards are available for sale. The 10 Mbps cards are not used anymore. Now-i-days 10/100, 10/100/1000 auto-sensing cards are available in the market. Everything is moving to dual mode auto-sensing technology. Even though Gigabyte Ethernet is getting more popular now-a-days, Gigabyte LANs are 10 times faster than a 100Mbps LAN. Ethernet was evolved from a protocol called ALOHA. ALOHA was mainly used in packet radio network which communicate using satellites. In brief, an earth station sends some data, as soon as the data is ready it waits for an acknowledgement (ACK). If it fails to get an ACK, it would time out and sends the same thing again. The sender keeps trying until the transmission is successful. The lesson to be learned here is that it is important to limit the number of users on a shared network medium. Traffic analysis can help determine the maximum number of users to ensure a reasonable Quality of Service (QOS).
LAN Advantages and Services
A LAN has the following advantages:
- They work on higher operating speed than WAN and MAN.
- They suit the requirements of a specific organization.
- They are easy to install and maintain.
- They exist as connected (wired) and wireless configurations.
LAN can provide the following services. They are:
(i) File-based service
Transfer of files from one node to another within the LAN area. For example, in a typical LAN used for local banking, the file containing the detailed transactions of a specific customer is transferred form sever to the client, whenever new transactions are made on behalf of the customer. It also provides efficient ways of storing and retrieving the data. When multiple copies of the same file exist, it provides necessary synchronization in updating the files. LAN also provides backup for the critical data so that safe recovery is possible when a failure occurs. It also provides data encryption facility to control the access to certain data to only selected persons.
(ii) Print services
There can be one or more printers, modems, and fax machines attached to a LAN and used by applications. A number of clients can share these devices. Print services allow many clients to safely share printers and other such devices. All modem LANs provide these services.
(iii) Application-based services
Applications run on a client may require higher computational capabilities. Servers are more powerful than the clients. In a LAN, more than one client can share the computational power of a server. Application servers are good examples for this.
(iv) Mail and message-based services
Electronic-mail is an important service used for exchanging information between people on a network. Mails can be stored or forwarded to another user. Many free mail servers are available on the Internet to provide free mail services to its clients.
(v) Database services
Storing and retrieving of data in databases is another requirement of a client to control and manipulate the data. Database servers are the most popular ones that service the need of clients.
(vi) Distributed data services
When data is distributed, it is possible for more than one client system to share the data. Though the databases appear physically distributed, there is a single logical view given by the database server. There are so many issues involved in sharing a single file by more than one client. Consistency issue is very seriously tackled when updating shared files.
(vii) Remote services
Linking a LAN with a remote computer or a mainframe is another service required. This feature is used to access remote databases available in large mainframes.
Characteristics of a LAN
A LAN can be characterized by means of hardware and software components and a set of protocols.
Hardware components of a LAN are:
-
The Server
Server is a computer that provides services to other computers (workstations or clients) on the network. The primary goal of a LAN server is data management. It stores, retrieves, and protects the data. A server also sends data to the requesters on the network and also to authorized remote users. The type and configurations needed for the server, depends mainly on the purpose for which the LAN is being constructed. Servers may be classified, based on the type of service they provide. A single server may provide a number of services also. The following are the list of servers categorized, based on the type of service.
(i) File server and disk server
A file server makes the disk storage space (in the order of several Gigabytes), to various client PCs. The file server satisfies the request for data from application programs running in client workstations. It also keeps the consistency of data when more than one client makes simultaneous data requests. In a LAN, working with a file server, all application running in a workstation may request for a file with involving the local operating system. The workstation sends its file request to the server and the server processes the request and sends the required file directly to the workstation.
(ii) Disk servers
Disk servers are similar to file servers. The difference is that, in a file server when an application running in a workstation requests for a specific file, the local operating system, running on the workstation interacts with the file server and gets the information required. In a disk server, the application can directly access the required file without the intervention of the local operating system.
(iii) Database server
These servers are a subset of the file server category. They provide access to huge databases for clients. Database information is stored in hard disk storage or CD ROM or optical disk drives. It contains the DBMS, which is more sophisticated than the basic file I/O access method. DBMS eliminates data redundancy and allows the user, transparent data distribution. The database server extracts only the relevant data and passes it to the requesting client, rather than passing the entire file like a file server.
(iv) Print server
Every LAN has one or more printers shared by all the nodes or workstations. The role of a print server is to collect the information from several workstations, store them on the disk and send it to the printer. This processing is known as print spooling. Print services become a part of the file server nowadays. In many LAN architectures, any PC on the LAN can act as a print server.
(v) Backup server
Such servers provide backup in case the main server fails. Every network must have a back up server to keep all the information safe. Periodically, these servers must be updated so that reliability can be improved.
(vi) Gateway server
A gateway server is used to provide connectivity to other networks. The GIAS (Gateway server of VSNL, India) is a gateway server, which provides connectivity to all other networks on the Internet for the Indian segment of the Internet. A gateway server also provides connectivity to dissimilar networks.
(vii) Communication server
Communication servers are more diverse than the other servers. The main functions of a communication server are linking client workstations on the LAN with mainframe computers, sharing a pool of modems among the client stations, and communicating with other LANs as well.
Examples of the most popular LAN servers are Novell Netware LAN Server, Microsoft Windows NT Server or Windows 2000, IBMOS2 Server, etc.
-
Workstations
Workstations or nodes are the clients that use the services provided by the network server. Workstations are loaded with special software to interact with the server to access the services. Examples of workstations include the Microsoft Windows NT workstation, Windows 2000 workstation, IBM workstation, Sun workstation, etc.
-
The Transmission Media for LAN
Various transmission media are used for constructing a LANs. The most popular among them are twisted pair, coaxial cable, or optical fibers. LANs operated with any such transmission media is known as wired LAN. LANs can also be constructed without a transmission media or cable. Such LANs are known as wireless LANs.
-
Communication Equipments
(i) Repeater
A repeater operates at layer-I. It has just enough intelligence to find out the layer-l incoming signals are and then send out a clean stream of signals built from scratch. Noise is eliminated from the signals in this manner. A repeater has one incoming and one outgoing line. It extends the distance that a signal may be sent over a transmission media.
(ii) Hub
A hub is a multi-port repeater. Any incoming signal is repeated on all other outgoing lines. A hub functions at layer-I.
(iii) Bridge
A bridge has more intelligence than a hub or repeater. This device separates two segments of a single LAN. A bridge operates at layer-2 by looking at the destination address in the frame header. Consulting a table, the bridge will determine if the frame needs to pass on to the other segment. Only certain frames may pass those with the correct MAC address.
(iv) Switch
A switch is a multi-port bridge. It performs its functions at layer two. It looks at MAC layer addresses just like a bridge, consults a table, and determines if a frame needs to be sent on one of the attached lines. Multiple connections can occur through a switch simultaneously as long as they don’t compete for the same line. A switch, just like a bridge, does not divide a LAN into two LANs. It merely reduces unnecessary traffic on LAN segments.
(v) Router
A router is more intelligent than bridges and switches. It functions at layer-3. At layer-2 all incoming frames are checked for errors and then they are delivered to layer-3. A layer-3 datagram has an address that permits it to be sent across internet works (interconnected networks). This requires a single global addressing scheme. The router finds the layer-3 address and consults a table that it keeps. There the router will learn which attached line to send the datagram on. A router provides facilities to the stations on the LAN, to access other networks.