Firewall is a network security system that monitors, filters, and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between trusted internal networks and untrusted external networks, such as the internet, to prevent unauthorized access and potential cyberattacks. Firewalls can be hardware-based, software-based, or a combination of both. They examine data packets, allowing only legitimate traffic while blocking malicious or suspicious activity. By enforcing access policies, firewalls protect systems from hackers, malware, and unauthorized users, ensuring data confidentiality, integrity, and availability within networks and computer systems.
Components of Firewall:
Packet filtering is a fundamental firewall component that examines data packets entering or leaving the network. It analyzes packet headers, such as IP addresses, port numbers, and protocols, to determine whether to allow or block the traffic based on predefined rules. This method is fast and efficient, but it cannot inspect the actual data content, making it vulnerable to advanced threats. Packet filtering works as the first line of defense, ensuring only traffic matching the organization’s security policies is permitted. While simple, it provides essential control over basic network traffic flow.
A proxy service acts as an intermediary between users and the internet. Instead of direct communication, the firewall’s proxy server fetches requests on behalf of the user, providing an additional security layer. It hides the internal network structure, preventing attackers from identifying devices within the system. Proxies can also perform deep packet inspection, cache frequently accessed content, and filter requests based on content or user behavior. By breaking direct connections, proxies reduce exposure to threats, enhance privacy, and enforce security policies, making them essential for controlling application-level communication.
Stateful inspection, also called dynamic packet filtering, monitors the state and context of active network connections. Unlike basic packet filtering, which checks packets in isolation, stateful inspection analyzes the entire traffic session, ensuring packets are part of a legitimate, established connection. It maintains a state table to track sessions and validates whether incoming packets match expected patterns. This prevents unauthorized attempts like spoofing or session hijacking. Stateful inspection provides a balance of strong security and performance, offering a more robust solution for modern networks compared to simple filtering techniques.
NAT is a firewall component that conceals internal IP addresses by translating them into a single public IP address for external communication. This masking improves security by hiding the network’s internal structure from outsiders. NAT also helps conserve limited IPv4 addresses by allowing multiple devices to share one public IP. In addition to protecting devices from direct external exposure, NAT ensures efficient traffic management. Combined with firewall rules, NAT minimizes the risk of attacks on internal systems, making it a critical function in safeguarding organizational networks from potential cyber intrusions.
Many firewalls include VPN support to establish secure, encrypted tunnels for remote access. VPN-enabled firewalls allow employees or authorized users to connect to the organization’s internal network safely over the internet. By encrypting traffic, VPNs ensure confidentiality, integrity, and authentication, protecting sensitive data from interception. They also enforce access control by verifying user credentials before granting entry. VPN integration in firewalls is especially important for organizations with remote workers, branch offices, or cloud-based operations, as it ensures safe communication and resource sharing while maintaining the network’s security perimeter.
Intrusion Detection and Prevention Systems (IDPS) in firewalls monitor network traffic for suspicious activity or policy violations. They use signature-based, anomaly-based, or behavioral techniques to identify threats like malware, denial-of-service attacks, or unauthorized access attempts. An IDS alerts administrators about suspicious events, while an IPS actively blocks or mitigates malicious traffic in real-time. Integrating IDPS with firewalls provides layered defense against both known and emerging cyber threats. This proactive security feature ensures threats are detected early, reducing damage and maintaining network integrity.
Logging and monitoring are essential firewall components that record details of all traffic and activities passing through the firewall. Logs include information such as source and destination IPs, ports, protocols, and timestamps of network events. These records help administrators analyze traffic patterns, detect anomalies, and investigate security incidents. Real-time monitoring enables quick response to attacks, while historical logs support audits and compliance requirements. By offering visibility into network behavior, logging and monitoring strengthen overall security posture, enabling organizations to improve firewall policies and anticipate potential threats more effectively.
Content filtering in firewalls controls access to inappropriate, harmful, or non-business-related websites and online resources. By inspecting web traffic, the firewall blocks access to sites containing malware, phishing, or offensive content, ensuring employee productivity and organizational safety. Content filtering can also restrict access based on categories like social media, streaming platforms, or gaming. It often integrates with URL filtering databases or keyword-based restrictions. Beyond security, content filtering helps organizations comply with regulations, maintain bandwidth efficiency, and protect users from harmful online material.
How does a Firewall Work?
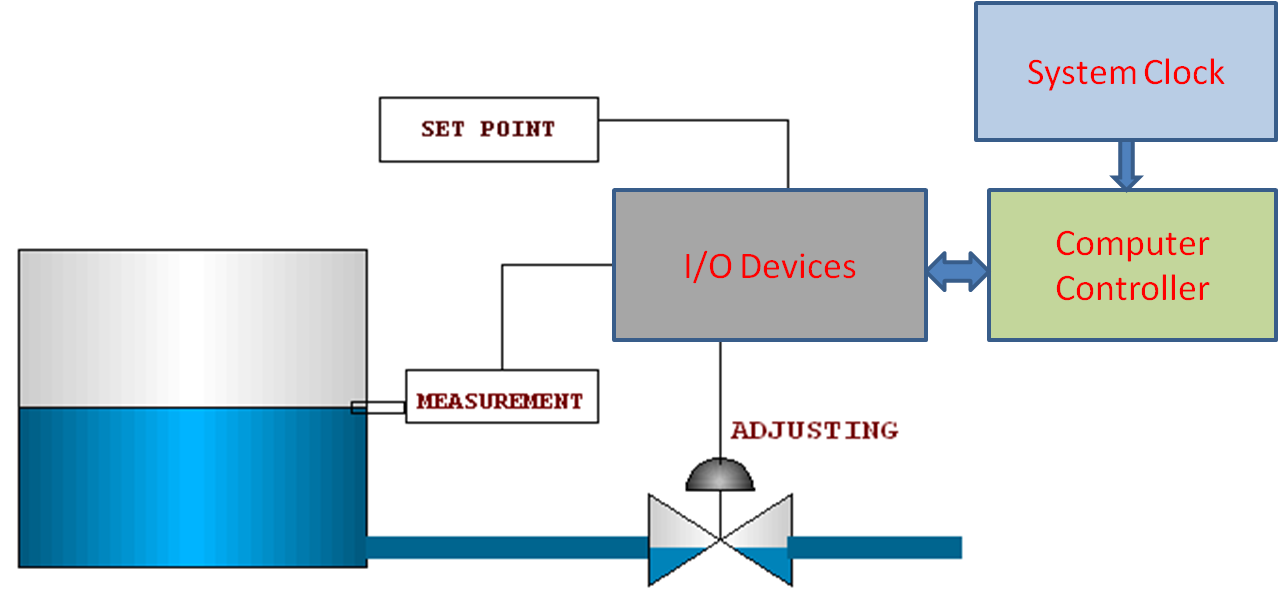
A firewall works by continuously monitoring all incoming and outgoing network traffic. It acts as a security guard, examining data packets that travel between a private network and external sources like the internet. Each packet is inspected based on pre-set rules such as IP addresses, port numbers, and protocols. If a packet meets the allowed criteria, it is permitted to pass; otherwise, it is blocked. This packet-filtering process ensures that only safe and authorized communication enters or leaves the network, providing a first line of defense against unauthorized access.
Firewalls enforce access control by defining which users, devices, or applications can interact with the network. Administrators configure policies that specify permitted services, such as web browsing or email, while restricting unwanted ones. By applying these rules, the firewall creates barriers between trusted and untrusted zones, ensuring critical systems are shielded. Access control may be based on IP addresses, domain names, or authentication credentials. This mechanism helps prevent attackers, malware, or unauthorized users from exploiting the network. Essentially, firewalls limit exposure by ensuring that only approved communication is allowed, maintaining both privacy and system integrity.
Modern firewalls use stateful inspection, a method that not only checks packet headers but also tracks the state of active connections. Instead of treating each packet independently, the firewall records session details in a state table. It verifies whether a packet belongs to an established, legitimate connection or is suspicious. For example, if a packet claims to be a response to a request but no such request was sent, the firewall will block it. This deeper inspection provides more accuracy and security than simple packet filtering, helping to detect and stop sophisticated cyberattacks effectively.
A firewall acts as a defense mechanism by blocking malicious traffic, viruses, worms, and hacking attempts before they reach the network. Many firewalls integrate intrusion detection, intrusion prevention, and content filtering to strengthen security. They can identify unusual patterns, such as port scanning or denial-of-service (DoS) attempts, and take immediate action. By controlling both inbound and outbound traffic, firewalls prevent sensitive data from being leaked or stolen. This multi-layered protection reduces vulnerabilities and ensures the confidentiality, integrity, and availability of network resources, making firewalls a critical safeguard in cybersecurity.
Types of Firewalls:
A packet-filtering firewall is the most basic type, which examines data packets moving across a network. It checks source and destination IP addresses, port numbers, and protocols against predefined rules. If the packet matches the rules, it is allowed; otherwise, it is blocked. This firewall works at the network layer and is efficient but limited because it does not inspect the content of packets. While it provides quick filtering, it is vulnerable to sophisticated attacks that disguise malicious data. It is best suited for small networks requiring simple, cost-effective protection without complex monitoring.
A stateful inspection firewall, also known as a dynamic packet filter, goes beyond simple packet filtering. It monitors active connections and keeps track of the state of network sessions using a state table. Instead of only checking packet headers, it verifies whether the packet belongs to an existing, legitimate session. This makes it more secure than basic firewalls, as it prevents malicious or unsolicited traffic. Stateful firewalls are commonly used in modern networks because they balance performance and security. They are effective in protecting against unauthorized access and attacks while still maintaining efficient traffic flow.
A proxy firewall acts as an intermediary between users and the internet by filtering requests at the application layer. Instead of allowing direct communication, it processes requests and forwards them to the destination on behalf of the user. This hides the internal network, offering strong anonymity and protection. Proxy firewalls can inspect data deeply, block harmful content, and prevent direct exposure to threats. However, they may slow down network performance due to heavy traffic inspection. They are useful in organizations needing strict security and monitoring, especially for web browsing, email filtering, and application-level access control.
Next-Generation Firewalls combine traditional firewall features with advanced capabilities like intrusion prevention systems (IPS), deep packet inspection, and application awareness. Unlike standard firewalls, NGFWs can identify and control applications regardless of port, protocol, or encryption. They also integrate features like malware protection, URL filtering, and threat intelligence. This makes them highly effective against sophisticated cyber threats. NGFWs provide greater visibility into network traffic, enabling organizations to enforce more granular security policies. Although costlier, they are widely adopted by enterprises that require robust, multi-layered security to protect against modern attacks and evolving cyber risks.
Challenges of Firewalls:
Firewalls are effective at blocking unauthorized access, but they cannot detect or prevent all types of cyber threats. They mainly monitor incoming and outgoing traffic, which means attacks like phishing, malware hidden in encrypted traffic, or insider threats may bypass them. Additionally, firewalls do not provide full protection against social engineering or sophisticated zero-day attacks. Relying solely on a firewall without other security measures creates vulnerabilities. To overcome this limitation, organizations must use firewalls in combination with intrusion detection systems, antivirus software, and strong user awareness programs to ensure a multi-layered defense strategy.
Firewalls, especially advanced ones like next-generation firewalls (NGFWs), can introduce latency by analyzing packets, inspecting content, and filtering applications. High traffic volumes may slow down network performance, causing delays for users and critical business applications. In environments with heavy data flow, this can impact productivity. To address this, organizations need robust hardware, proper configuration, and network optimization strategies. However, upgrading infrastructure increases costs. Balancing strong security with optimal performance remains a challenge, as overloading the firewall or misconfiguring rules may lead to bottlenecks, service disruptions, or even security gaps if traffic inspection is reduced to improve speed.
Setting up and maintaining a firewall requires skilled administrators to configure rules, policies, and filters correctly. Misconfigured firewalls may either block legitimate traffic, causing disruptions, or allow malicious traffic, creating security holes. Large organizations with complex networks face challenges in managing multiple firewalls across different locations. Regular updates and monitoring are necessary to keep policies aligned with evolving security threats. Inadequate documentation or improper rule prioritization may result in conflicts and vulnerabilities. To overcome this, organizations must invest in trained professionals, automation tools, and consistent auditing practices to ensure firewalls function effectively without compromising usability or security.
While basic firewalls are affordable, advanced solutions like next-generation firewalls (NGFWs) come with high costs for acquisition, deployment, and maintenance. Additionally, they require powerful hardware, constant updates, and skilled IT staff for monitoring. Smaller organizations often struggle with these expenses, making them more vulnerable to cyberattacks. Furthermore, as threats evolve, firewalls need regular upgrades, which add to long-term costs. Cloud-based firewalls may reduce infrastructure expenses but still involve subscription fees. Balancing cost-effectiveness and strong security remains a major challenge, especially for businesses with limited budgets that cannot afford enterprise-grade firewall solutions with advanced threat protection.
Like this:
Like Loading...